Point-of-Sale Password Recovery⚓︎
Difficulty:
Direct link: santashop website
Terminal hint: Linux Primer
Objective⚓︎
Request
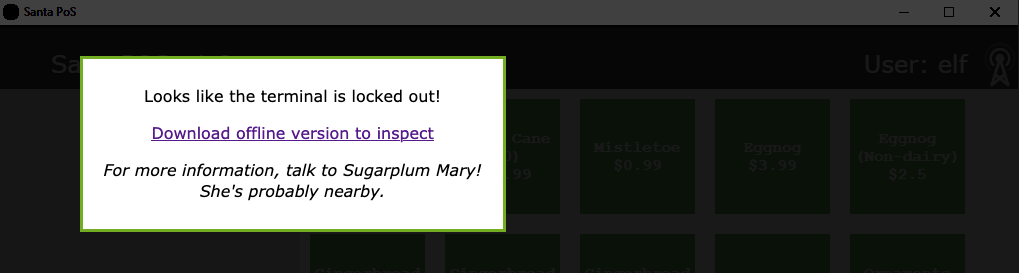
Help Sugarplum Mary in the Courtyard find the supervisor password for the point-of-sale terminal. What's the password?
Sugarplum Mary
Hey, wouldja' mind helping me get into my point-of-sale terminal?
It's down, and we kinda' need it running.
Problem is: it is asking for a password. I never set one!
Can you help me figure out what it is so I can get set up?
Shinny says this might be an Electron application.
Hints⚓︎
Electron ASAR Extraction
There are tools and guides explaining how to extract ASAR from Electron apps.
Electron Applications
It's possible to extract the source code from an Electron app.
Solution⚓︎
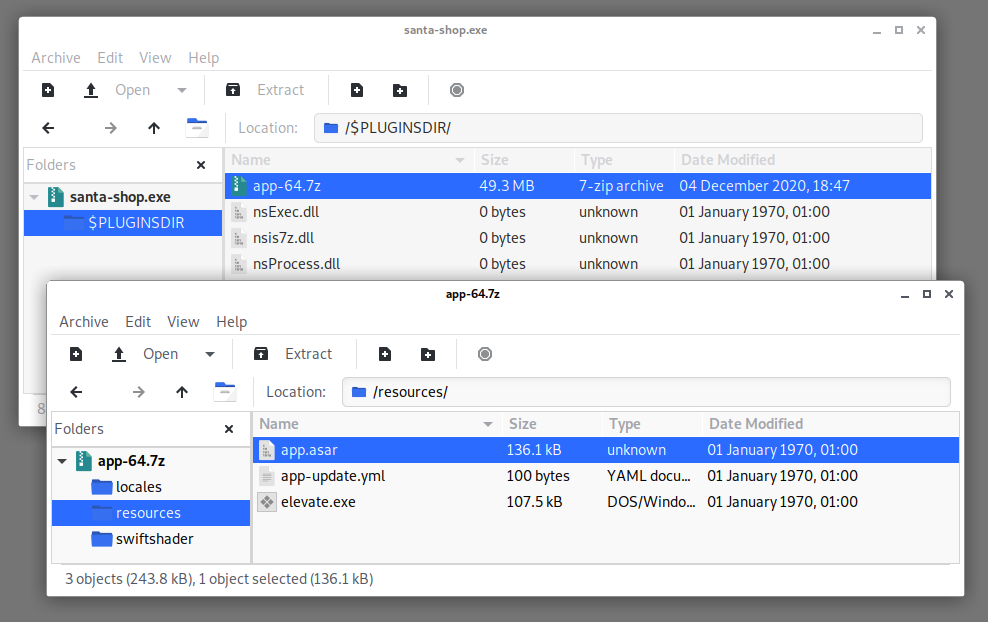
Download the santa-shop.exe binary using the link provided on the santa-shop website. The file command tells us it's a Windows executable (thanks Captain Obvious) and a Nullsoft Installer self-extracting archive, which means we can extract the contents using pretty much any capable archive manager. 7-Zip on Windows, Engrampa on Kali Linux, and The Unarchiver on macOS all work. Inside the binary you'll find a 7-zip archive named app-64.7z. Extract that as well.
The app.assar archive file is what we're looking for. While the hints provided by Sugarplum Mary point to a tool and a guide on how to extract these types of archives, all we really need is grep -a pass app.asar to search for lines containing the string pass.
Asar file format
Asar is a simple extensive archive format, it works like tar that concatenates all files together without compression, while having random access support.
Concatenating plaintext and binary files together doesn't modify the data. In other words, because no compression is being applied, any plaintext information that goes into the Asar archive remains plaintext and will be searchable. The -a parameter forces grep to treat the whole file as ASCII text and print any matching lines to the command line.
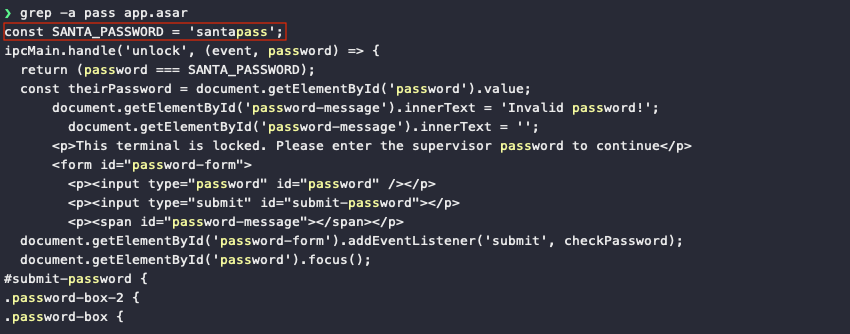
Answer
santapass