Redis Bug Hunt⚓︎
Elf: Holly Evergreen
Direct link: redis terminal
Objective: Broken Tag Generator
Request⚓︎
Holly Evergreen
Hi, so glad to see you! I'm Holly Evergreen.
I've been working with this Redis-based terminal here.
We're quite sure there's a bug in it, but we haven't caught it yet.
The maintenance port is available for curling, if you'd like to investigate.
Can you check the source of the index.php page and look for the bug?
I read something online recently about remote code execution on Redis. That might help!
I think I got close to RCE, but I get mixed up between commas and plusses.
You'll figure it out, I'm sure!
Hints⚓︎
Redis RCE
This is kind of what we're trying to do...
Solution⚓︎
Welcome message
We need your help!!
The server stopped working, all that's left is the maintenance port.
To access it, run:
curl http://localhost/maintenance.php
We're pretty sure the bug is in the index page. Can you somehow use the
maintenance page to view the source code for the index page?
The solution is based on the Webshell example in the Redis pentesting guide provided by Holly Evergreen. We need to trick Redis into creating a PHP script in the web server root folder that reads and writes the contents of index.php to a non-PHP file (so we can retrieve it without the contents being parsed by the PHP interpreter).
We could use the suggested curl approach, but then we'd need to URL-encode any special characters so they are properly parsed by the maintenance.php script before being forwarded to the redis-cli command line tool. Since /etc/redis/redis.conf contains the password in cleartext anyway (i.e., R3disp@ss), we can use redis-cli directly instead.
Redis DB compression
Ensure that rdbcompression is disabled in /etc/redis/redis.conf. Saving the Redis database to disk with compression enabled will also compress the PHP code stored inside the DB, making the code unreadable for the PHP interpreter and preventing the PHP instructions from being executed.
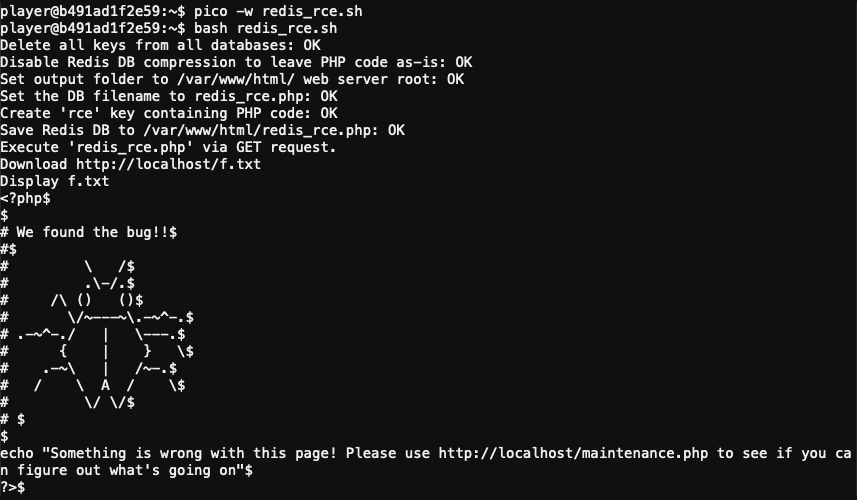
To automate the process create a redis_rce.sh script containing the following commands.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 | |
Execute the redis_rce.sh script on the host to find the bug.
Response⚓︎
Holly Evergreen
See? I knew you could to it!
I wonder, could we figure out the problem with the Tag Generator if we can get the source code?
Can you figure out the path to the script?
I've discovered that enumerating all endpoints is a really good idea to understand an application's functionality.
Sometimes I find the Content-Type header hinders the browser more than it helps.
If you find a way to execute code blindly, maybe you can redirect to a file then download that file?